Cybersecurity
- Home /
- Categories /
- Cybersecurity
Infrastructure Enumeration: Mapping the Target
Before you can hack a target, you must understand it. Learn the principles of infrastructure enumeration, from DNS and cloud resources to OSINT and staff profiling.
Read More
SQL Injection for Scummies
Learn everything about SQL injection attacks - from basic concepts to advanced exploitation techniques and prevention methods. A comprehensive guide for cybersecurity enthusiasts.
Read More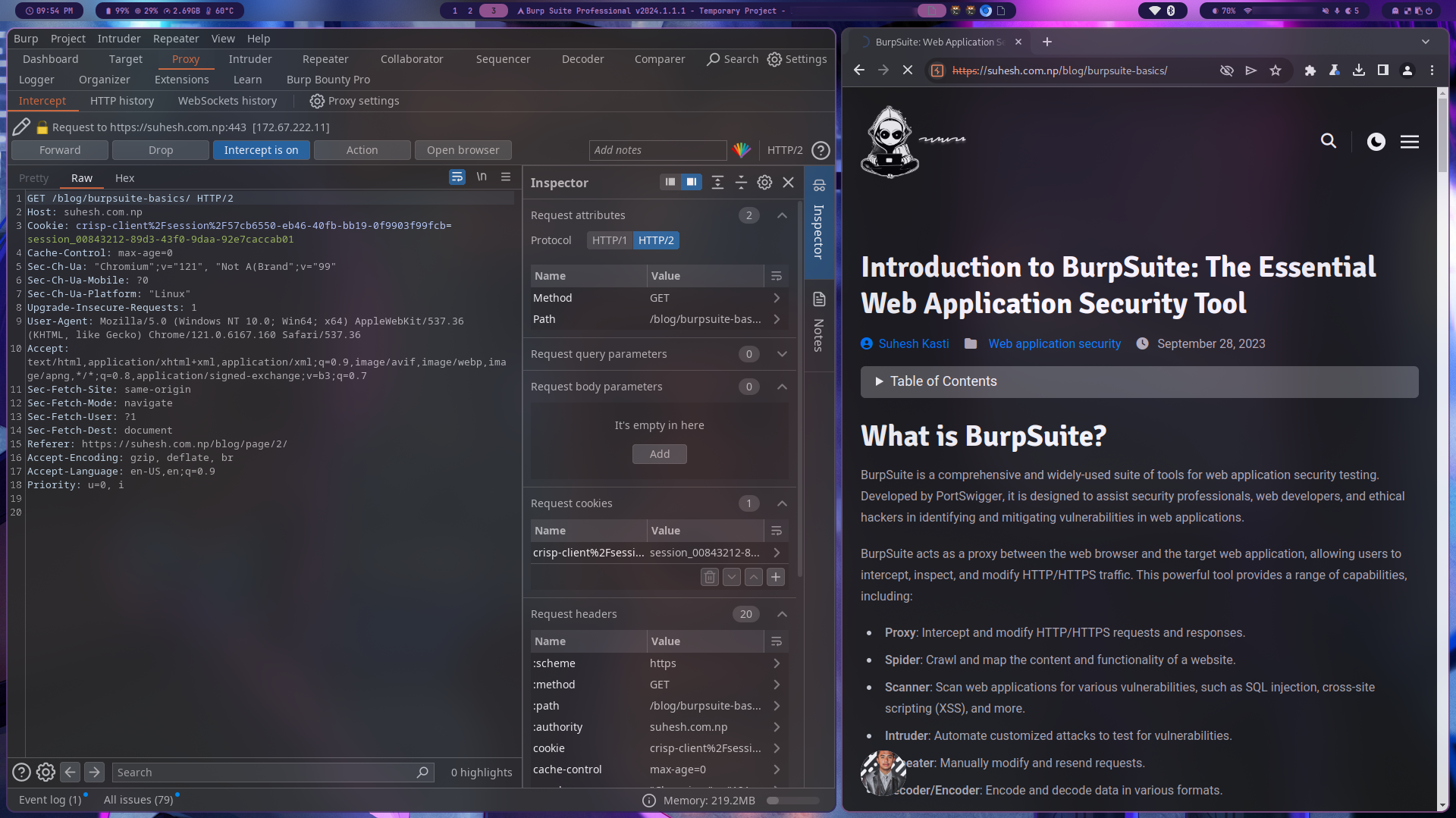
BurpSuite: Part 1
Discover BurpSuite, a powerful tool for web application security testing, and learn about its features, use cases, and an open-source alternative called OWASP ZAP.
Read More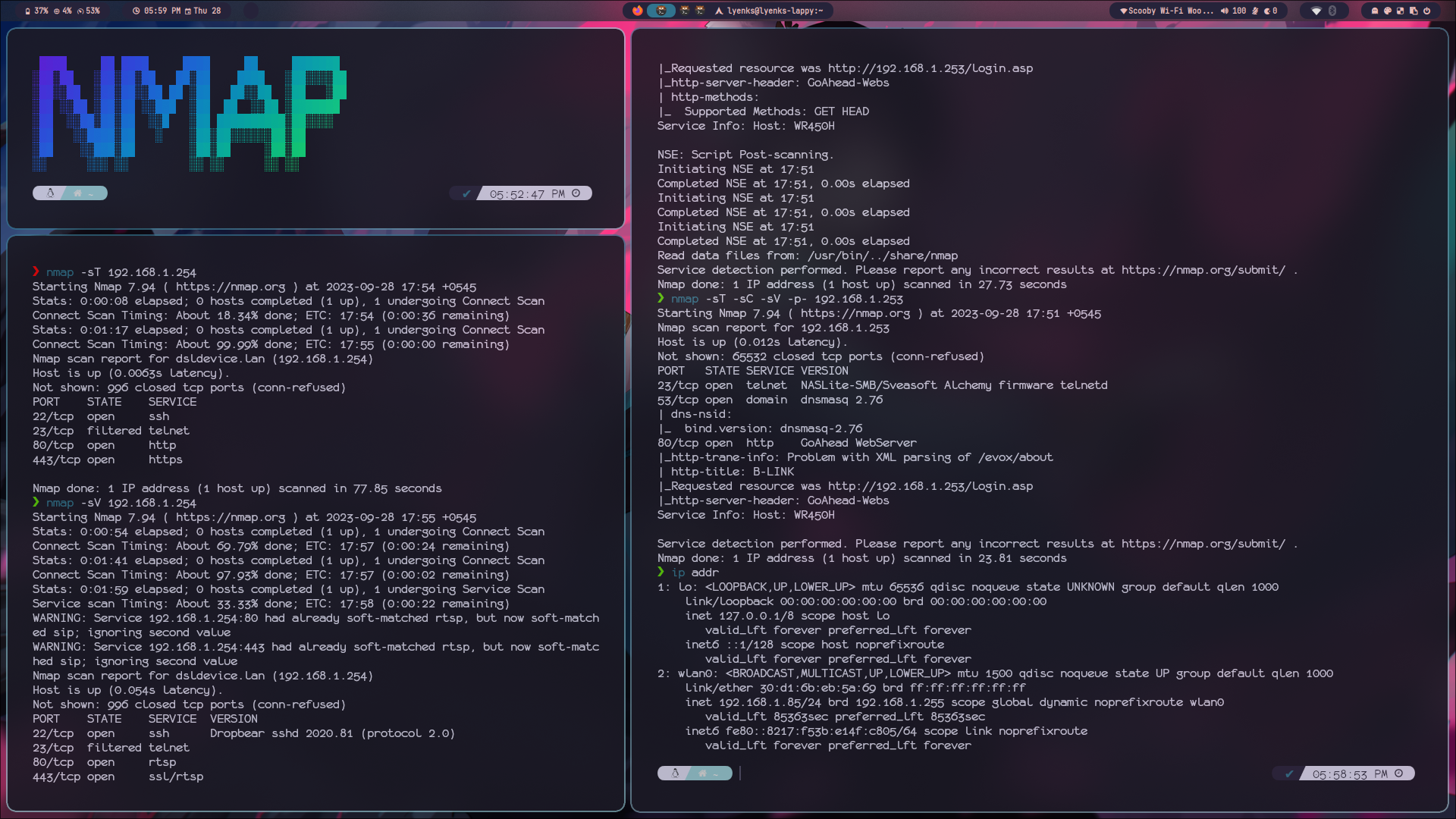
Exploring Nmap: Part 1
Every hacking starts with enumeration and reconnaissance phase. Enumeration is a crucial step in the information-gathering process and Nmap is one of the most powerful enumaration tool.
Read More