Bug Bounty
- Home /
- Categories /
- Bug Bounty
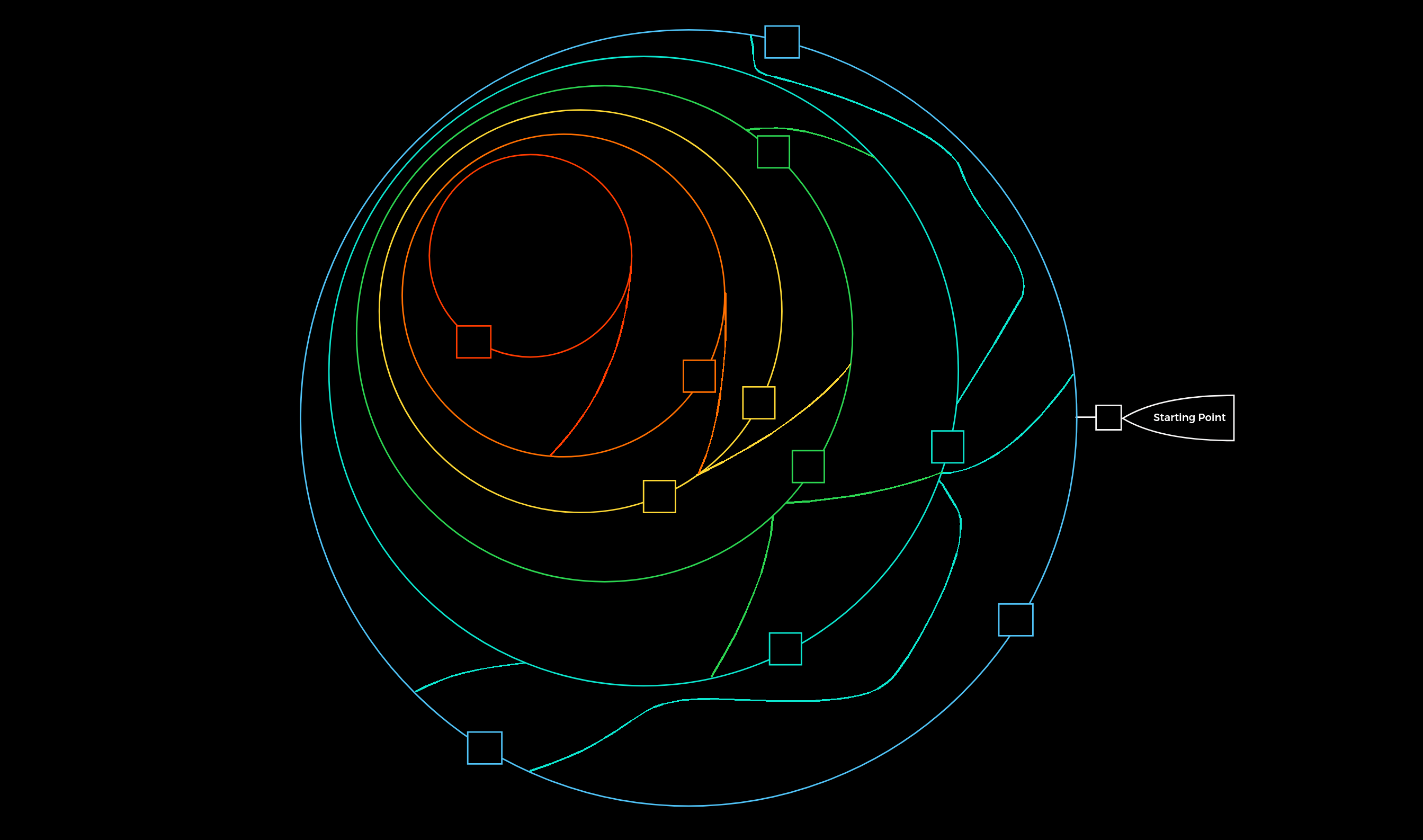
Infrastructure Enumeration: Mapping the Target
Before you can hack a target, you must understand it. Learn the principles of infrastructure enumeration, from DNS and cloud resources to OSINT and staff profiling.
Read More