Blog Posts
- Home /
- Blog Posts
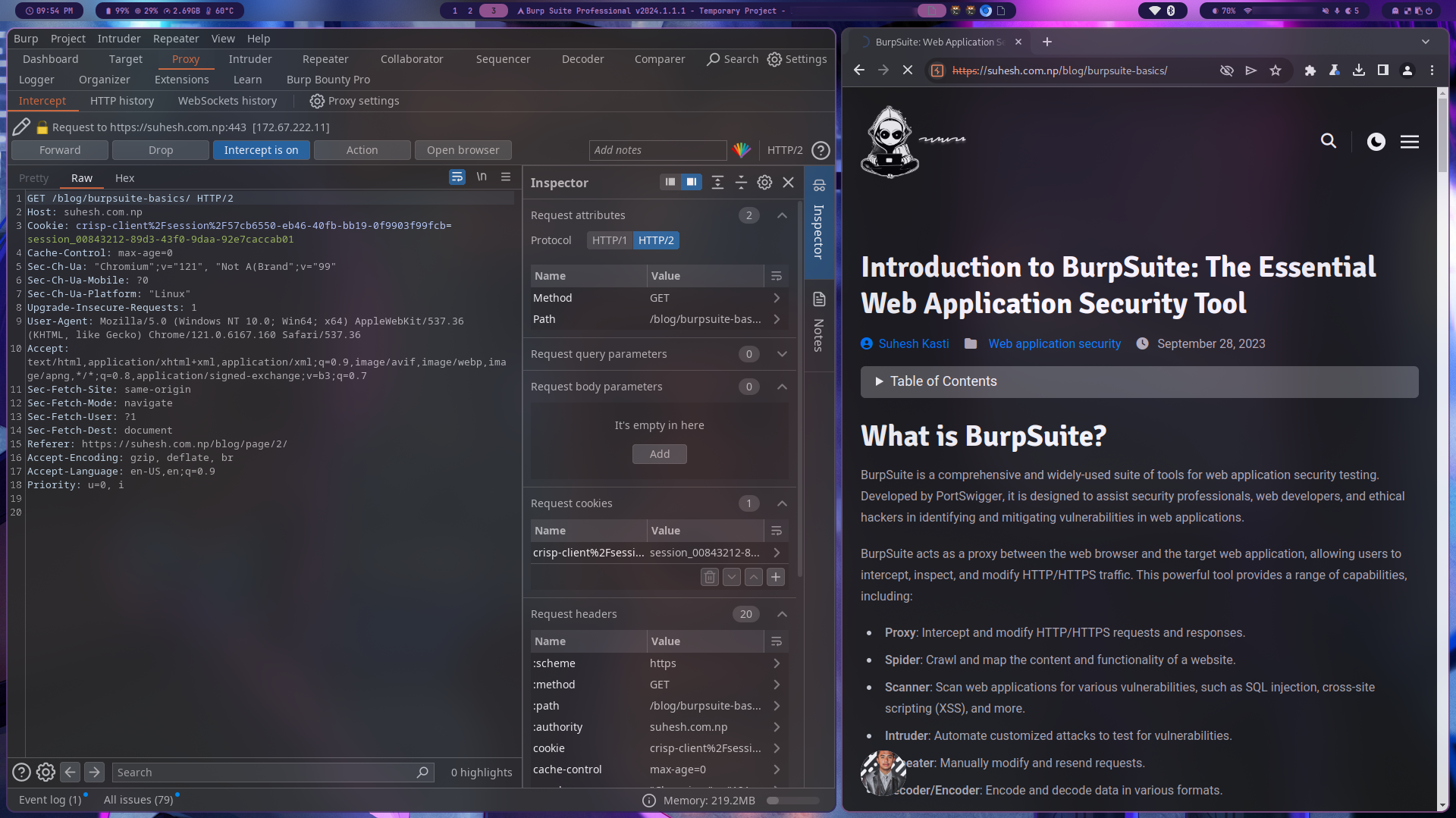
BurpSuite: Part 1
Discover BurpSuite, a powerful tool for web application security testing, and learn about its features, use cases, and an open-source alternative called OWASP ZAP.
Read More
Deploying to Cloudflare
If you are a beginner frontend developer, this is a goldmine for you. Host your website projects for free in cloudflare pages easily and shine infront of your competition in recruitments.
Read More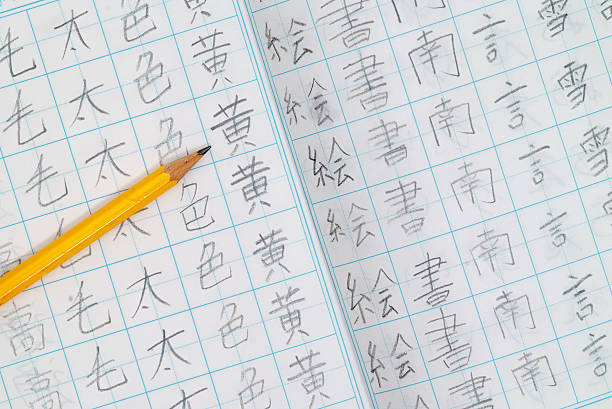
My path to gain fluency in Japanese
🔠 Unearth the intricate characters that form the backbone of Japanese writing. Unlock the magic behind each stroke and immerse yourself in the rich history of this captivating script.
Read More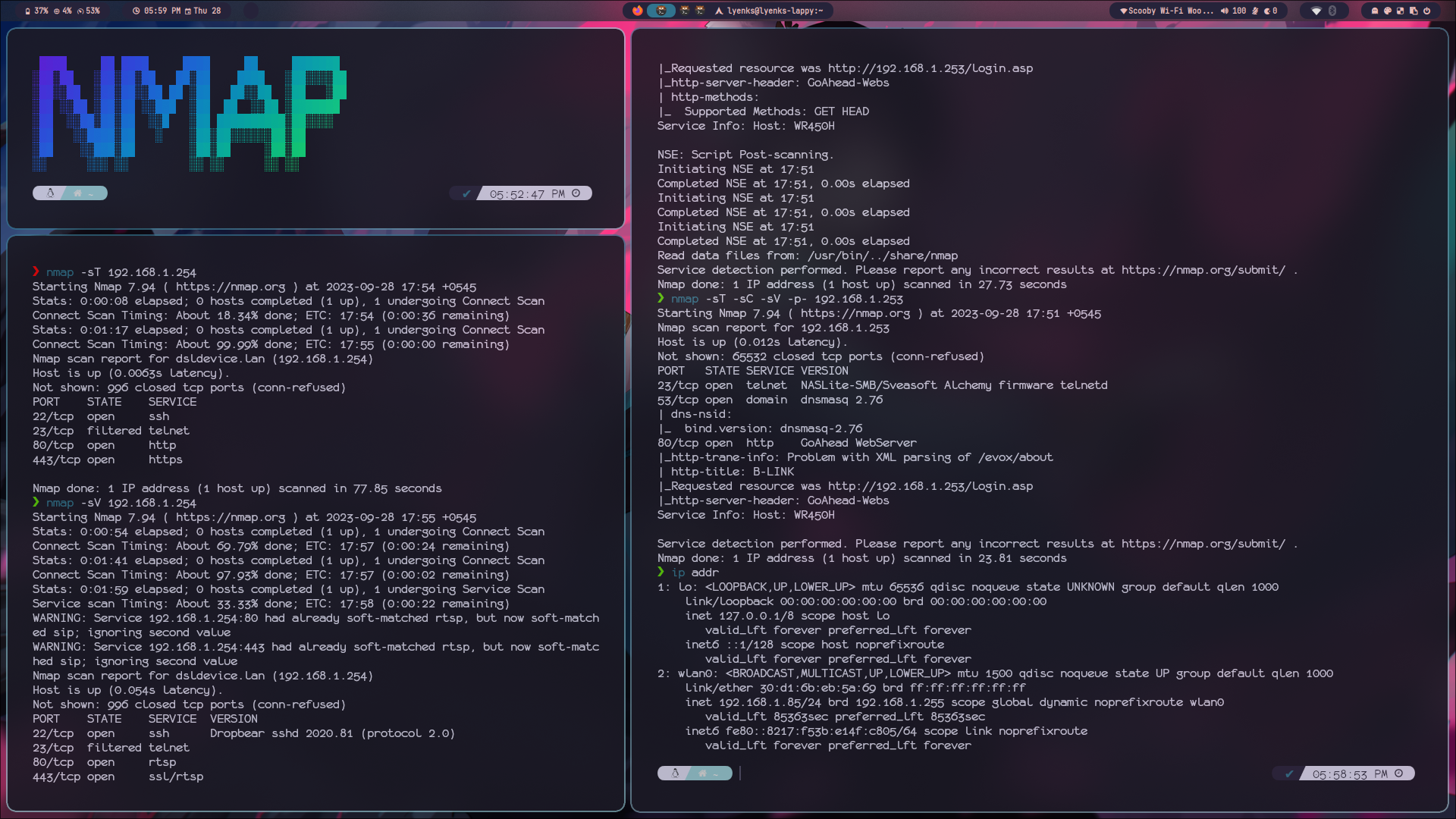
Exploring Nmap: Part 1
Every hacking starts with enumeration and reconnaissance phase. Enumeration is a crucial step in the information-gathering process and Nmap is one of the most powerful enumaration tool.
Read More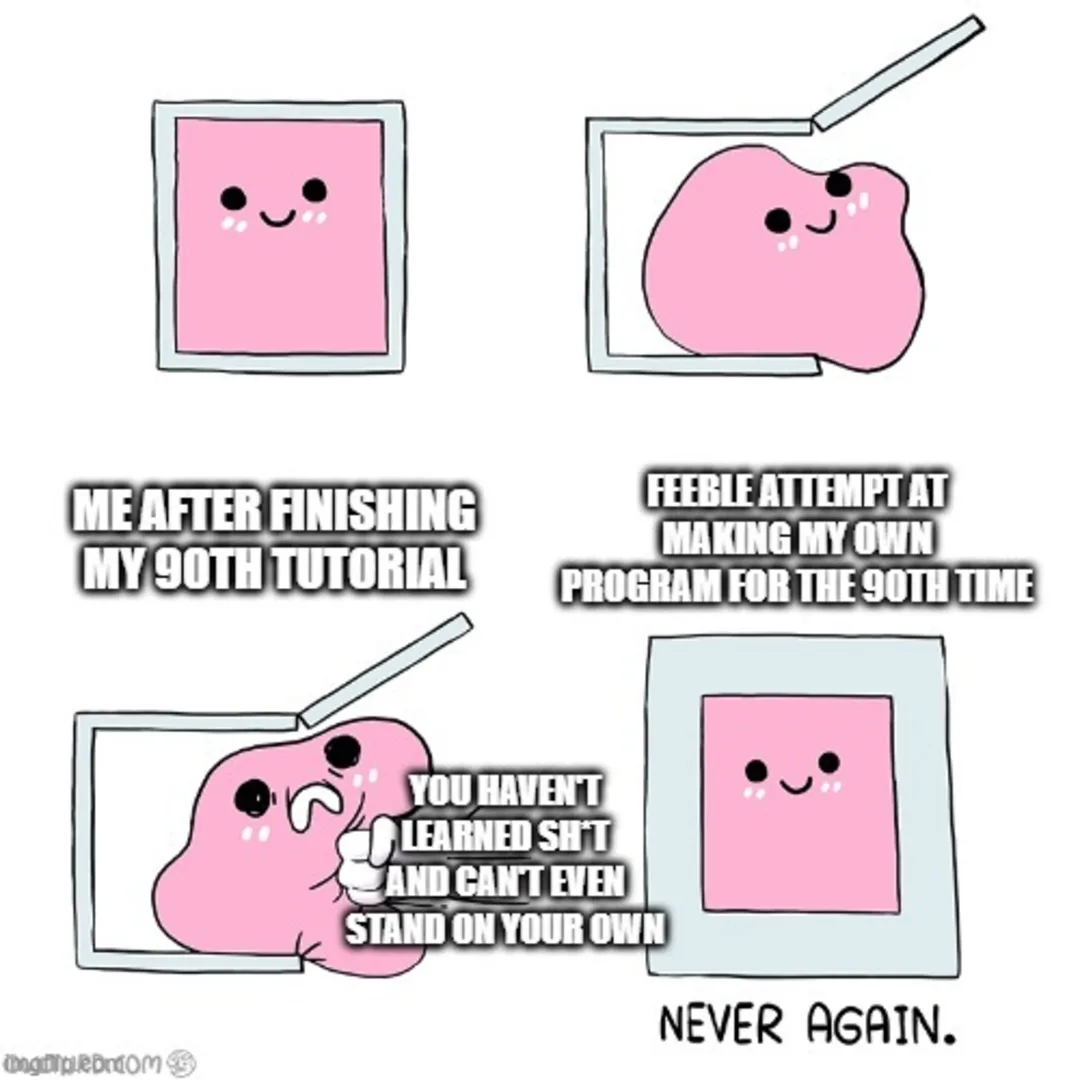
Breaking Free from Tutorial Overload
Breaking Free from Tutorial Overload: A simple guide to learning successfully and stop being on a learning treadmill but not moving forward
Read MoreExplore Other Content
From Today I Learned
Categories
Tags
- Application Centric Interface (ACI)
- Application Policy Infrastructure Controller(APIC)
- BurpSuite
- Cloud Security
- Coding
- CPTS
- Deployment
- Direct Server Return
- DNS
- Enumeration
- Evasion
- F5 101
- F5-BigIP
- Git
- Github
- Hack the Box
- Half Proxy
- Hiragana
- Hosting
- Katakana
- Khanji
- Load Balancer
- Network Automation
- Network Planes
- Nmap
- OSI
- OSINT
- Overlay
- OWASP
- Penetration Testing
- Port Scanning
- Programming
- Proxy
- Python
- Reconnaissance
- Red Team
- Software Defined Network(SDN)
- SQL Injection
- Static Sites
- TCP/IP
- Tutorial Hell
- Underlay
- Version Control System
- Virtual Extensible LAN (VXLAN)
- Vulnerability Scanning
- Web App Security
- Web Security
- Webapp Firewall