Blog Posts
- Home /
- Blog Posts
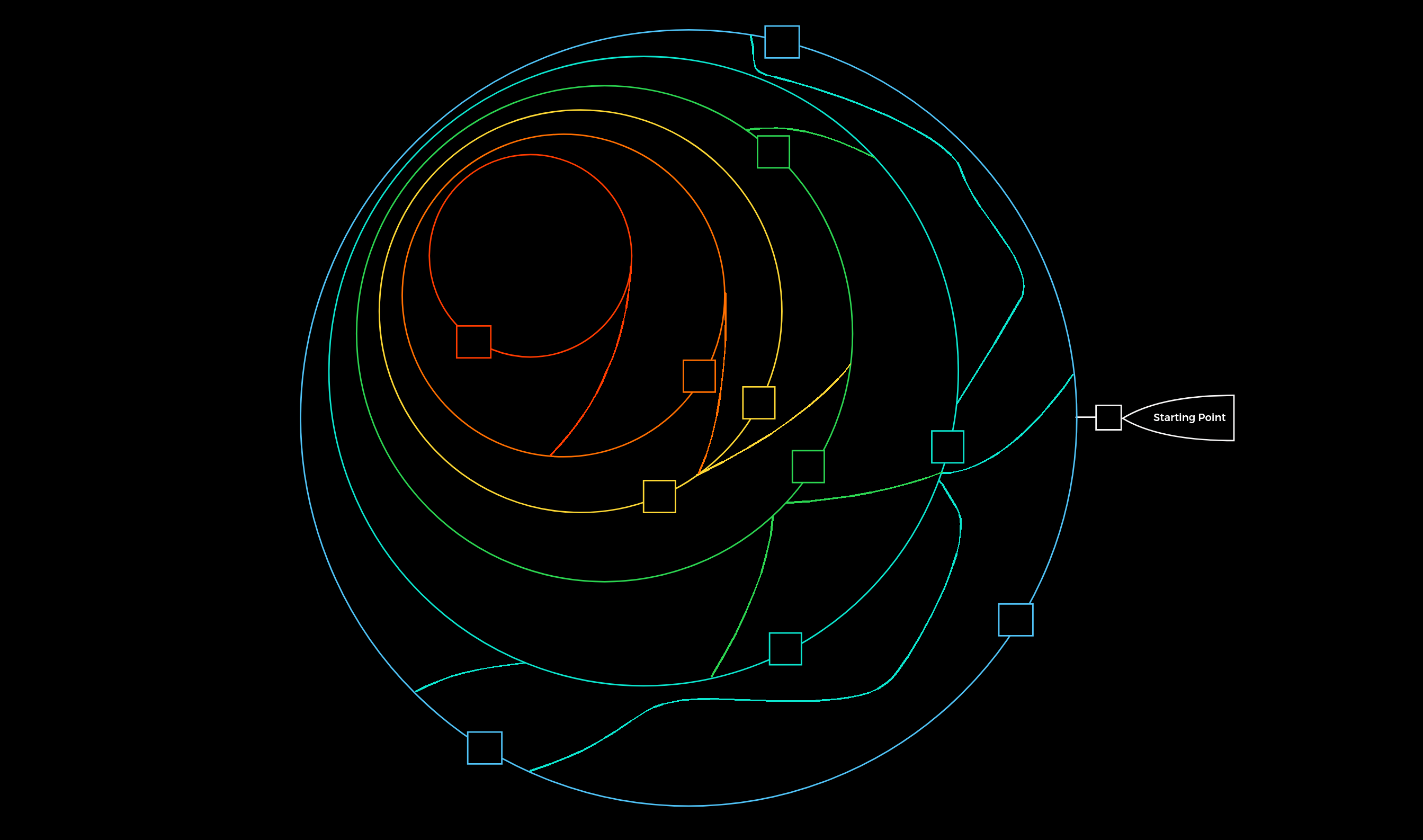
Infrastructure Enumeration: Mapping the Target
Before you can hack a target, you must understand it. Learn the principles of infrastructure enumeration, from DNS and cloud resources to OSINT and staff profiling.
Read More
CPTS: Network Enumeration with Nmap
Comprehensive guide to mastering Nmap for Hack The Box CPTS. Covers Host Discovery, UDP scanning headaches, NSE scripting, Firewall/IDS evasion, and custom ZSH automation for extracting ports.
Read More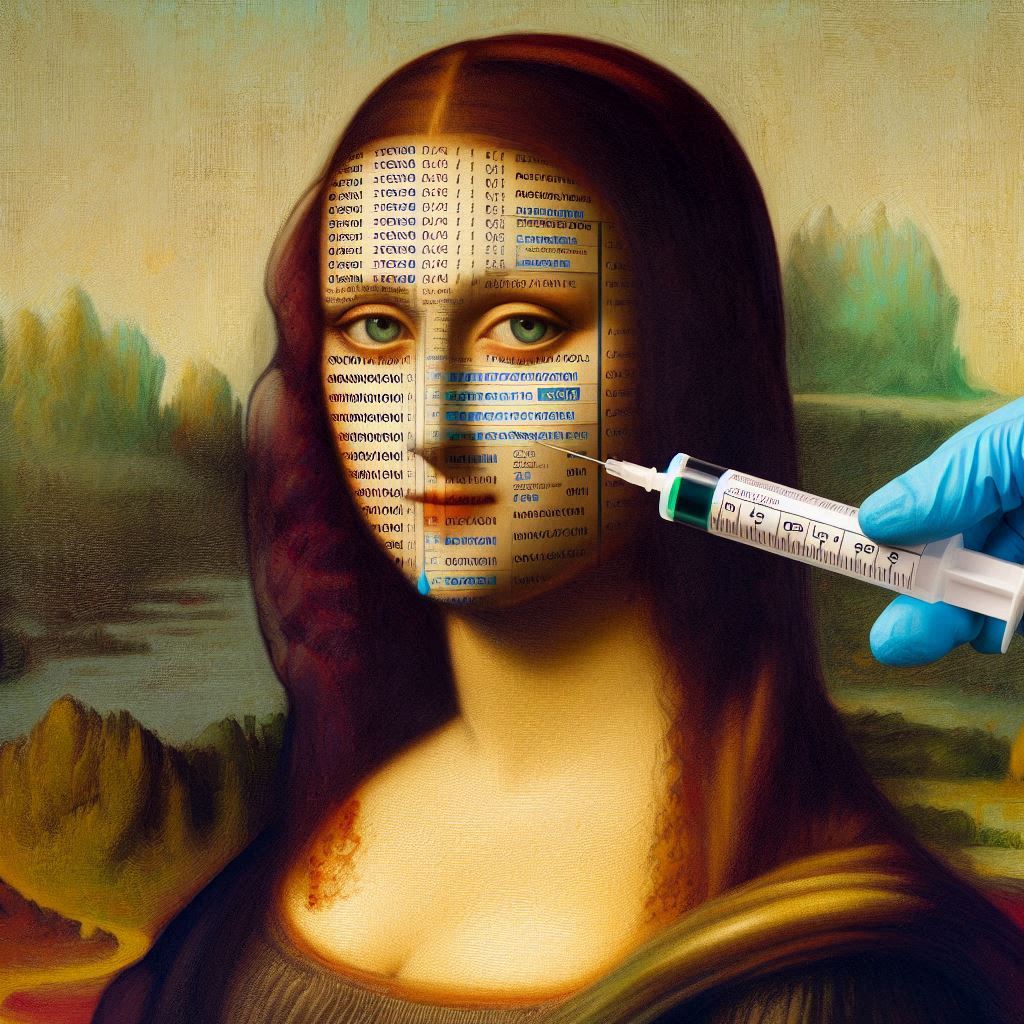
SQL Injection for Scummies
Learn everything about SQL injection attacks - from basic concepts to advanced exploitation techniques and prevention methods. A comprehensive guide for cybersecurity enthusiasts.
Read More
DNS for Dummies: Part 3
In this part we will be getting our hands dirty and setting up our own personal DNS server using an ubuntu virtual machine.
Read More
DNS for Dummies: Part 2
Taking a deep dive into the journey of a DNS query, understanding recursive and authoritative servers, common DNS records, and the underlying technical mechanisms.
Read More
DNS for Dummies: Part 1
The journey to mastering DNS starts here. Let's discover why DNS is the internet's backbone and its role in enabling modern-day connectivity.
Read MoreExplore Other Content
From Today I Learned
Categories
Tags
- Application Centric Interface (ACI)
- Application Policy Infrastructure Controller(APIC)
- BurpSuite
- Cloud Security
- Coding
- CPTS
- Deployment
- Direct Server Return
- DNS
- Enumeration
- Evasion
- F5 101
- F5-BigIP
- Git
- Github
- Hack the Box
- Half Proxy
- Hiragana
- Hosting
- Katakana
- Khanji
- Load Balancer
- Network Automation
- Network Planes
- Nmap
- OSI
- OSINT
- Overlay
- OWASP
- Penetration Testing
- Port Scanning
- Programming
- Proxy
- Python
- Reconnaissance
- Red Team
- Software Defined Network(SDN)
- SQL Injection
- Static Sites
- TCP/IP
- Tutorial Hell
- Underlay
- Version Control System
- Virtual Extensible LAN (VXLAN)
- Vulnerability Scanning
- Web App Security
- Web Security
- Webapp Firewall